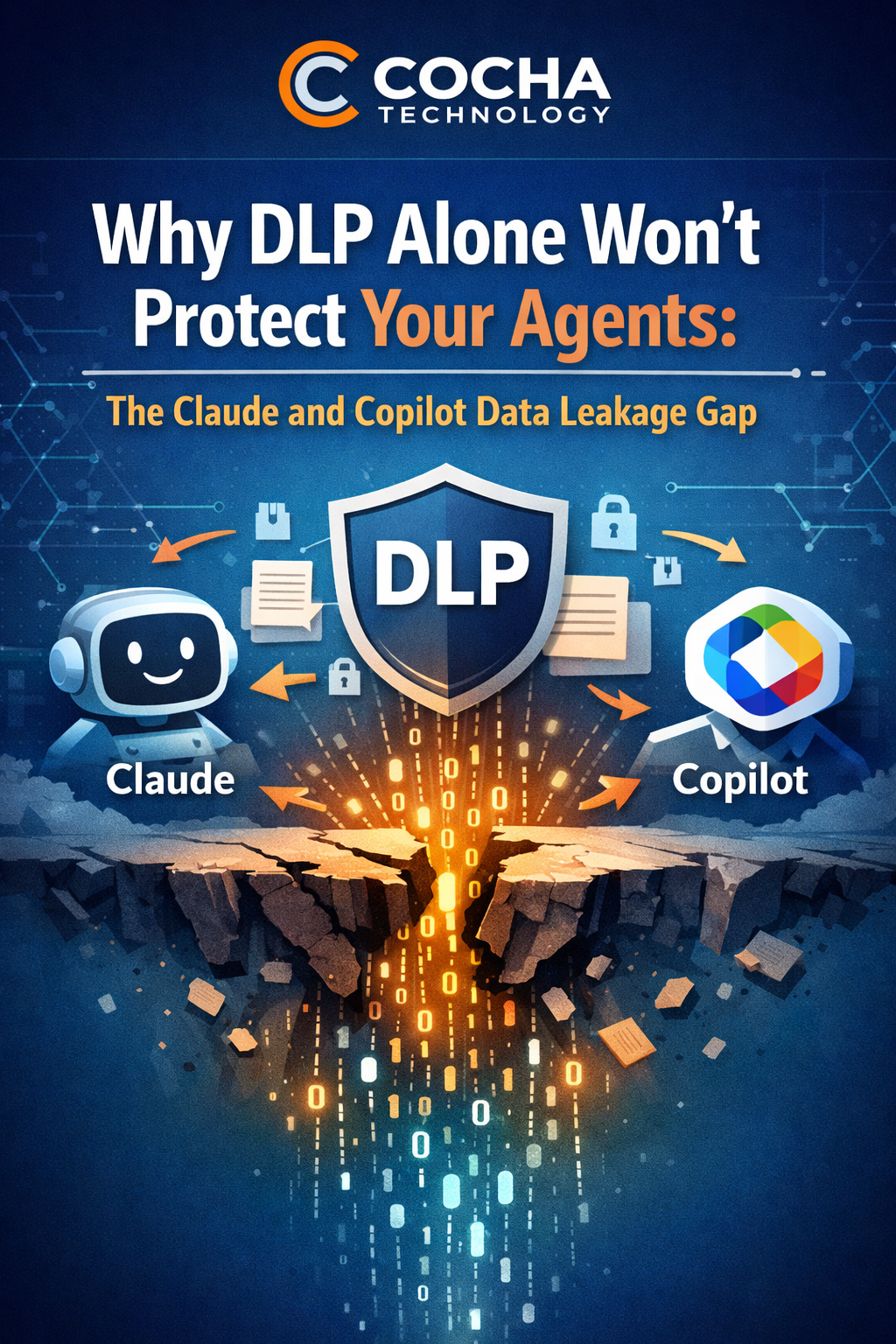
Why DLP Alone Won’t Protect Your Agents: The Claude and Copilot Data Leakage Gap
April 13, 2026
Your DLP tool is working perfectly. It blocks employees from uploading files to personal cloud accounts. It flags emails with credit card numbers. It alerts when someone tries to print a document marked confidential. It is doing exactly the job it was built to do.
The problem is the job it was built to do.
Data loss prevention was designed for a world where humans make conscious decisions to move data. A human decides to attach a file to an email. A human decides to copy a folder to a USB drive. A human decides to upload a document to a personal account. DLP watches for those decisions and applies policy rules to them.
Agents do not make decisions. They access data continuously, in the background, through permissions they inherit from the users who deploy them. They extract patterns, summarize documents, and surface insights — and most DLP tools have no category for any of it.
This is not a configuration problem. You cannot fix it by tightening your DLP policies. It is an architectural gap between what DLP was designed to protect against and how agents actually operate. Every organization deploying Claude or Microsoft Copilot is sitting inside that gap right now.
How DLP Works — and Why Agents Break It
Traditional DLP is a rules-based system built on a specific assumption: that data loss happens when a human moves data from a controlled location to an uncontrolled one. Copy, upload, email, print — these are the actions DLP monitors. When a human performs one of these actions on sensitive data, DLP either blocks the action, logs it, or alerts a security team.
This model works well for what it was designed to address. An employee copying a client list to their personal Google Drive will trigger DLP if the policy is correctly configured. An email with a social security number will get flagged. A document marked “confidential” that someone tries to upload to Dropbox will be blocked.
The model fails completely when the data never moves.
Agents operate in what security practitioners call “data in context” — not data in motion or data at rest in the traditional sense, but data that is accessed, processed, and synthesized within its existing location. An agent connected to your SharePoint environment does not copy your files anywhere. It reads them where they live. It builds a model of their contents. It uses that model to generate responses to the person using the agent.
Gartner’s 2025 Market Guide for Data Loss Prevention makes this limitation explicit, noting that traditional DLP solutions focus on content and are data-centric, which means they cannot easily distinguish between authorized data access and the kind of continuous, systematic access that agents perform.
The result is a coverage gap that most organizations do not know exists until something goes wrong.
Consider a concrete scenario. A finance analyst at a professional services firm has access to salary data, budget files, and financial projections as part of their role. They connect Microsoft Copilot to their work account to help with report drafting. Copilot now has access to everything the analyst can access. The analyst asks Copilot to help analyze compensation trends. Copilot pulls from salary files the analyst technically has access to but had never opened. It generates a summary. DLP sees nothing unusual — the analyst has permission to access those files, no data left the environment, no policy was triggered.
But sensitive compensation data was just surfaced to a person who had permission to access it technically, but probably should not have had those permissions at all. And it happened because an agent was thorough in a way humans typically are not.
The Three Ways Agents Leak Data Despite DLP
1. Permission-based access at scale:
Agents inherit user permissions and operate on all of them simultaneously. A human with overprivileged access to sensitive data is limited by time and attention — they can only read so many files, and they generally only read files relevant to their current task. An agent has no such limitations. It accesses everything it can reach, systematically, as part of its normal operation.
This is not technically data leakage in the traditional sense. No data left the controlled environment. But the agent has now processed and indexed data far beyond what the user would have accessed manually — and it uses all of that context when responding to queries. The exposure is not in the data moving out. It is in the insights moving in.
2. Summarization and insight extraction:
DLP is designed to detect sensitive data patterns — social security numbers, credit card numbers, specific document classifications. It is not designed to detect the meaning extracted from a document.
When an agent summarizes an M&A pipeline, it does not reproduce the documents. It extracts the strategic intent — the targets, the pricing rationale, the timeline, the negotiating position. None of that content pattern-matches against a DLP rule. But the insight is just as sensitive as the underlying data, and it has now been surfaced to anyone who asks the right question of the agent.
An agent trained on personnel files can reveal hiring strategy, compensation benchmarks, and performance patterns without ever reproducing a single piece of data that would trigger a DLP policy.
3. Context leakage through conversation:
When an agent explains its reasoning or cites what informed its response, it reveals the structure and sensitivity of the data it accessed. “Based on the quarterly projections in your finance SharePoint site…” tells the user both that the site exists and that the agent has indexed it. “Your HR team’s notes from last month indicate…” reveals that HR notes exist, where they live, and that the agent can read them.
This kind of context leakage is invisible to DLP. No sensitive data pattern was transmitted. But the user — and potentially anyone watching that conversation — now knows things about your organization’s data structure and content that they may not have known before.
"DLP protects against humans moving data. Agents don't move data. They just access everything they can reach and use it to answer questions. That's a gap DLP was never designed to close."
What Your AI Readiness Assessment Should Include
The gap between DLP coverage and agent risk is not theoretical — it is measurable. And measuring it is the first step toward closing it.
An AI readiness assessment maps exactly where your current security posture succeeds and fails when agents enter the picture. It does not replace your DLP tool. DLP is still necessary for all the human behaviors it was designed to address. But it adds the layer of visibility and control that DLP cannot provide.
The assessment should cover six areas.
First, your DLP policy audit. Not just whether policies exist, but whether they apply to agent behaviors. Most DLP policies were written before agents were a consideration. They address human actions with specific data types. They do not address continuous data access by an agent operating with inherited permissions.
Second, your data estate visibility. What data can agents currently reach in your environment? Most organizations do not know the answer to this question. They know what their policies say should be accessible, but not what is actually accessible given the current state of their permissions.
Third, your access control architecture. Do you have any controls specific to agent behavior, or do agents inherit all user permissions with no restrictions? Most organizations today are in the second category.
Fourth, your monitoring gaps. What does your current logging capture about agent activity? Can you tell, right now, which files a specific agent accessed in the last 30 days? In most organizations, the answer is no.
Fifth, your compliance framework alignment. Do your current security controls meet the requirements your industry framework puts on AI systems? NIST, SOC 2, and industry-specific frameworks increasingly address AI governance. Most organizations have not mapped their controls against these requirements.
Sixth, your remediation priorities. What are the three things you need to fix in the next 90 days to close the most significant gaps? An assessment without prioritization is just a list of problems
Your DLP is probably missing everything your agents are doing. Find out what it’s not catching.
Building the Foundation for Safe Agent Deployment
The answer to the DLP gap is not to stop deploying agents. Agents deliver real value — faster document review, better research synthesis, more efficient client communication. The firms and organizations that learn to deploy them safely will have a genuine competitive advantage.
The answer is to recognize that agent security requires a different foundation than the security architecture most organizations already have.
That foundation starts with visibility. You need to know what your agents can access before you can control what they access. That means a data estate analysis — mapping your actual permission structure, not the permission structure you intended to build.
It continues with controls designed specifically for agent behavior. Permission scoping that limits agents to specific data sets rather than all data the user can access. Monitoring that captures agent activity rather than just human activity. Governance policies written with agents in mind.
And it requires compliance alignment — understanding what your regulatory framework expects from an organization that deploys AI, and making sure your controls actually deliver it.
DLP is a necessary part of this architecture. It is not sufficient for it. Cocha Technology’s AI Readiness Assessment is designed to show you exactly where the gap is in your specific environment — and what to close first.
Your DLP tool is not failing. It is doing exactly what it was designed to do. The problem is that agents operate in ways DLP was never designed to address, and the gap between those two realities is where your data exposure lives.
Our AI Readiness Assessment maps that gap — your specific DLP coverage, your data estate risk, your agent-accessible data, and the 90-day remediation plan to start closing it. Ninety minutes of your time. Findings within five business days.
Schedule your free AI Readiness Assessment. Know exactly where your DLP ends and your agent risk begins.
Recent Posts
Have Any Question?
Call or email Cocha. We can help with your cybersecurity needs!
- (281) 607-0616
- info@cochatechnology.com
About the Author:

Steve Combs
Co-Founder & Managing Director, Cocha Technology
Steven is a fractional CIO/CISO with 30+ years of enterprise IT and security leadership. He has built AI governance frameworks for organizations with 1,700+ users, led enterprise Microsoft Copilot deployments, and conducted security assessments across law firms, energy companies, financial institutions, and PE-backed manufacturers.

