Agent Security Posture as an M&A Risk Factor
April 22, 2026
Your acquisition process is six months away. Your investment bankers are preparing the materials. Your management team is building the presentation. Everyone is focused on the financial story — revenue growth, margin expansion, the strategic rationale.
Meanwhile, the buyer’s technology due diligence team is building a different list.
It used to focus on technical debt, cloud migration readiness, and cybersecurity posture. Those three questions are still there. In 2025, a fourth has joined them with material weight: what is your AI and agent security readiness, and can you demonstrate it?
This is not a hypothetical future concern. PE acquirers — particularly those executing operational improvement theses that depend on post-acquisition efficiency gains — now include agent readiness in their technology evaluation because their post-close integration plans assume agent deployment. If you cannot demonstrate that your environment is ready for agents to be deployed safely, you are creating a contingency that will appear in the valuation.
Getting ahead of this question is not just a compliance exercise. It is a strategic advantage in a negotiation.
Why PE Buyers Now Care About Agent Security
Private equity acquisition theses have always included operational efficiency as a value creation lever. The specific tools have evolved — ERP standardization in one era, cloud migration in another, automation in another. Today’s tool is agents.
PE firms executing operational improvement strategies plan to deploy AI agents post-close to reduce headcount in repetitive functions, accelerate document processing, improve client communication, and extract operational data for better decision-making. This is the playbook. It is being executed across portfolio companies in every sector.
But agent deployment is not a plug-and-play operation. Deploying agents into an environment with overprivileged accounts, unsecured cloud infrastructure, and no data governance is not faster than doing it into a well-prepared environment — it is dangerous. And when it goes wrong, the operational efficiency gains the acquirer planned for do not materialize on schedule.
This is why the technology due diligence conversation now includes agent readiness. Buyers are not asking because they want to check a box. They are asking because the answer affects whether their post-close integration plan works.
The specific questions sophisticated PE technology teams now ask fall into four categories.
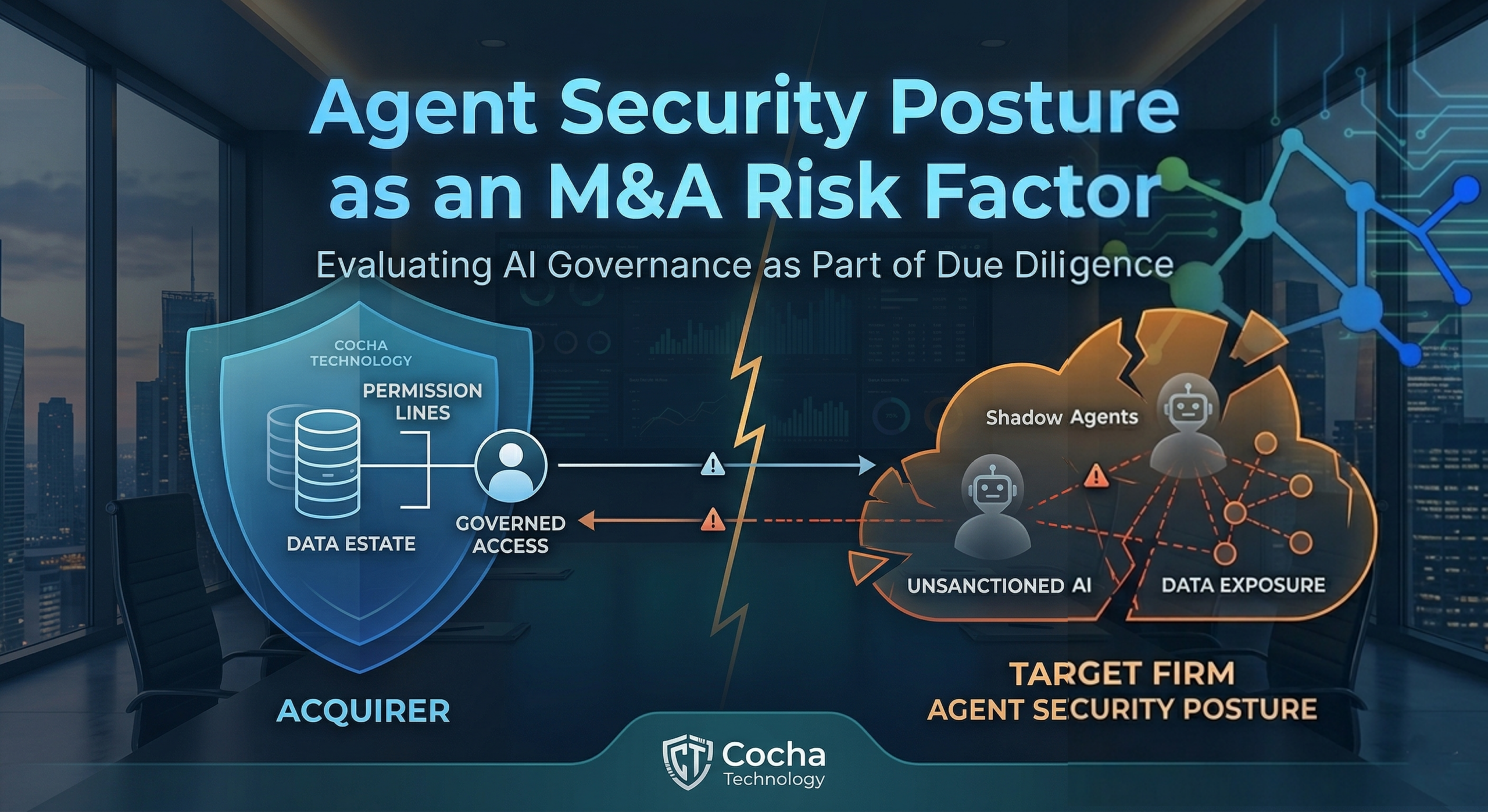
Data governance: Do you have visibility into your data estate? Can you demonstrate what data agents would be able to access if deployed today? Is there a governance framework that would control what agents can reach?
Access controls: Do you have a zero trust architecture or a documented path toward one? Have you conducted a permission audit? Can you demonstrate that your accounts follow least-privilege principles?
Cloud security: Have your cloud environments been assessed for misconfigurations? Is your infrastructure in a state where agents can be safely deployed?
AI readiness: Have you formally assessed your environment for agent-specific risks? Do you have policies governing AI tool use? Can you demonstrate that shadow AI is being managed?
If the answer to any of these questions is “no, we haven’t addressed that yet,” the buyer has a decision to make: price that work into the acquisition, require it as a pre-close condition, or accept it as post-close risk. None of those outcomes are better for the seller than having done the work beforehand.
Agent Security as a Material Risk Factor
The framing that matters for PE transactions is materiality. Not every technology gap is material. A slightly outdated ERP version is a nuisance. Cybersecurity vulnerabilities that could result in a data breach are material. Agent security that blocks post-close operational plans is material.
Agent security posture becomes material in a PE transaction when two conditions are met. First, the buyer’s value creation plan includes agent deployment as a significant operational lever. Second, the target’s environment is not ready to support safe agent deployment.
When both conditions are met, the acquirer faces a concrete, quantifiable problem: the operational efficiency gains they planned for will be delayed while the environment is brought to a state that supports agent deployment. That delay has a cost — in time, in spend on remediation, and in foregone efficiency gains.
The response from sophisticated acquirers is one of three options. They require the seller to remediate before close, which adds time and cost to the process. They adjust the purchase price to reflect the remediation cost. Or they require funds to be held in escrow pending completion of remediation post-close.
Companies that walk into due diligence with documented, third-party-validated agent readiness assessments remove this friction entirely. They answer the question before it is asked. They demonstrate operational maturity. They remove a contingency that would otherwise appear in the deal structure.
Companies that have not just assessed but actually remediated the gaps identified in their assessment are in an even stronger position. They can demonstrate not just awareness but action — which is the evidence that actually moves negotiations.
"PE buyers are not asking about agent security because they want to check a box. They are asking because the answer tells them whether their post-close plan will work."
What Smart PE-Backed Companies Are Doing
The companies that navigate PE transactions most effectively on the technology dimension share a common characteristic: they are proactive. They identify what the buyer’s due diligence will ask, answer those questions before the process starts, and walk into negotiations with documentation rather than explanations.
On agent security specifically, this means three things.
First, conducting a third-party assessment before the buyer asks. An independent assessment — conducted by someone who is not the company’s IT team — carries evidentiary weight that internal documentation does not. It demonstrates that the company did not just believe their environment was ready; they verified it.
Second, remediating the material gaps the assessment identifies. Not all gaps require remediation before close — some can be documented as known issues with a clear post-close plan. But gaps that are directly in the path of the buyer’s agent deployment plan should be addressed. Showing up to due diligence with a completed remediation is materially different from showing up with a gap list.
Third, documenting the process. The assessment report, the remediation actions taken, the current state of the environment — this documentation is the evidence package that answers the buyer’s technology due diligence questions before they are asked.
For companies that are six to twelve months from a transaction, this timeline is achievable. The assessment takes ninety minutes and delivers findings within five business days. Remediation of the highest-priority items typically takes two to three months. Documentation of the completed work is the natural output of the process.
For companies that are three months or fewer from close, we can expedite the assessment and reporting to match the due diligence timeline. The focus shifts to identifying and documenting the material items — the gaps that will appear in the buyer’s list — and either remediating them or building a documented, credible remediation plan.
Your acquirer will ask about agent security. Get ahead of the question before due diligence starts.
Proving Your Readiness Before Due Diligence
The evidence package that demonstrates agent readiness in a PE transaction has four components.
A data estate assessment — showing that you understand what data your environment contains, how it is structured, and what an agent would access. The Exposure Snapshot produces this.
An AI readiness assessment — showing that you have evaluated your current security posture against agent-specific risks and understand where your DLP and monitoring fall short. The AI Readiness Assessment produces this.
A zero trust assessment — showing that you have evaluated your permission structure, identity verification posture, and access controls against the requirements for safe agent deployment. The Zero Trust Assessment produces this.
Remediation documentation — showing what gaps you found and what you did about them. This is the work that happens between the assessments and the transaction.
Together, these four components answer the buyer’s question before it is asked. Not just “have you thought about this?” but “here is what we found, here is what we fixed, and here is what our environment looks like today.”
That is a fundamentally different conversation than walking into due diligence hoping agent security does not come up.
Agent security is a material due diligence issue in PE transactions today. Buyers are asking. Valuations are being affected. The gap between companies that have addressed this and companies that have not is measurable in deal structure, price, and closing timeline.
The path forward is straightforward: assess, remediate, document. Start now if your transaction is within the next year.
If you are planning an M&A process, schedule your agent readiness assessment before the buyer’s due diligence team asks the questions. Let’s discuss your timeline and what the assessment will reveal for your specific environment.
Recent Posts
Have Any Question?
Call or email Cocha. We can help with your cybersecurity needs!
- (281) 607-0616
- info@cochatechnology.com
About the Author:

Steve Combs
Co-Founder & Managing Director, Cocha Technology
Steven is a fractional CIO/CISO with 30+ years of enterprise IT and security leadership. He has built AI governance frameworks for organizations with 1,700+ users, led enterprise Microsoft Copilot deployments, and conducted security assessments across law firms, energy companies, financial institutions, and PE-backed manufacturers.

