FREE ASSESSMENT
Your DLP Is Working. Your Agents Are Not Protected.
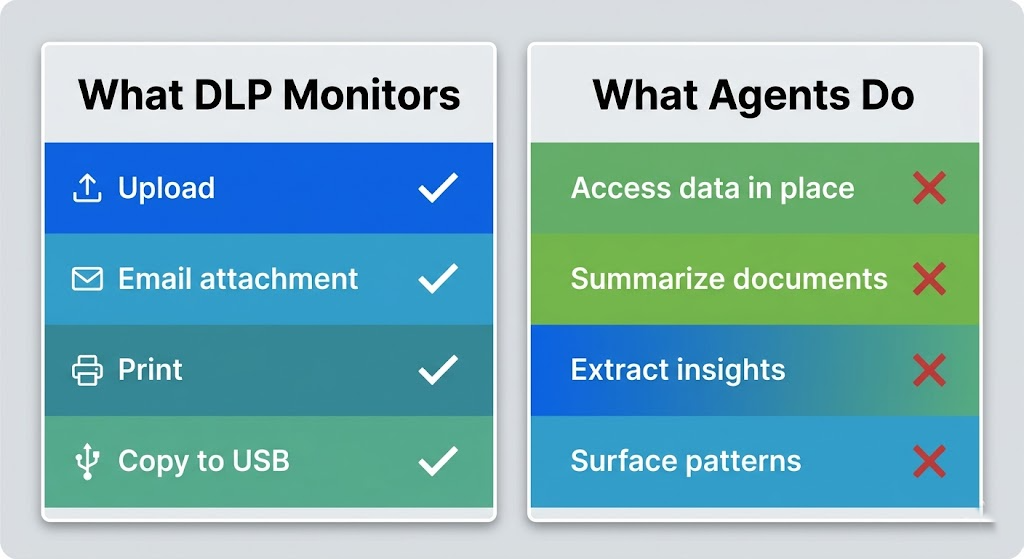
Traditional data loss prevention was designed for humans making conscious decisions to move data. Agents don't work that way. They access, summarize, and extract insights continuously — and most DLP tools see none of it.
See how it works ↓
✓ No software to install
✓ 90 minutes of your team’s time
✓ Findings report within 5 business days
Identifying Exposure
35%+
of DLP implementations fail to prevent data loss
Source: CrowdStrike / Industry Research
80%+
of workers use unapproved AI tools at work
Source: UpGuard, November 2025
38%
of employees share sensitive data with AI without approval
Source: CybSafe / NCA, 2024
$650k
average cost of an AI-associated data breach
Source: IBM Cost of a Data Breach Report 2024
The DLP Paradox
Your DLP Tool Is Working. That's Not the Problem.
Your DLP policy blocks employees from uploading files to personal cloud accounts. It flags emails with credit card numbers. It alerts when someone tries to print a confidential document. It’s doing exactly what it was designed to do.
The problem is what it was designed to do.
Traditional DLP assumes a human is making a conscious decision to move data. It watches for specific actions — upload, email, print, copy — and applies rules to those actions. It works because humans are the variable it was built to manage.
Agents are not humans. They don’t upload files. They don’t send emails with attachments. They connect to your environment, inherit the permissions of the user who deployed them, and then access data continuously in the background. They extract insights, summarize documents, and generate responses — and your DLP tool has no category for any of it.
This is not a flaw in your DLP setup. It’s a fundamental architectural gap. And every organization deploying Claude or Copilot is sitting inside it right now.
The Three Ways Agents Leak Data Despite Your DLP
Permission-Based Access
Agents inherit user permissions. If a user can access sensitive data, so can the agent. DLP has no mechanism to distinguish between what a user intends to access and what an agent accesses on their behalf. A finance analyst with access to salary data who connects an agent to their SharePoint gives that agent access to every salary record — because technically, the user has permission.
Insight Extraction
Agents don't need to move a file to leak information. They extract patterns and insights from data that individually would never trigger a DLP rule. No file was downloaded. No email was sent. But the strategic intent, the competitive positioning, the personnel decisions — all of it surfaces in the agent's responses to whoever asks the right question.
Context Leakage Through Conversation
When an agent explains its reasoning or cites sources, it reveals the structure and sensitivity of your data to the person using it. An agent trained on HR files doesn't leak a document — it reveals that certain documents exist, where they live, and what patterns they contain. Your DLP saw nothing.
What Your AI Readiness Assessment Includes
The Assessment Covers:
- DLP Policy Audit — We review your current DLP policies and map exactly which agent behaviors they cover and which they miss. Most organizations discover coverage gaps they didn’t know existed.
- Data Estate Visibility — We identify what data your agents can currently reach through your Microsoft 365 environment, including data users don’t actively think about.
- Access Control Review — We examine whether your current permission structure allows for agent-specific controls, or whether agents inherit all user permissions with no restrictions.
- Monitoring Gap Analysis — We identify what agent activity your current logging and monitoring captures — and what it doesn’t. If an agent is compromised, can you reconstruct what it accessed?
- Compliance Framework Mapping — We map your current posture against applicable frameworks (NIST, SOC 2, industry-specific) and identify where agent deployment creates compliance exposure.
- Prioritized Remediation Roadmap — Every finding is ranked by risk and paired with a specific, actionable fix. You leave with a clear 90-day plan, not a list of problems.
After Your Assessment, You'll Know:
- Exactly which data your agents can access today
- Where your DLP fails against agent-specific behavior
- What compliance frameworks require from your organization
- Your data estate risk score
- The specific gaps that matter most for your situation
- A 90-day roadmap to close them

How the Assessment Works
We Schedule
You fill out the form below. Steven reaches out within 24 hours to schedule your 90-minute assessment session at a time that works for your team. No software to install, no prep work required.
We Assess
In a 90-minute working session, we review your current DLP policies, data estate structure, agent deployment status, and monitoring coverage. We ask direct questions and document what we find.
We Deliver
Within 3–5 business days, you receive a written findings report with your risk score, gap analysis, and prioritized remediation roadmap. We walk you through it on a 30-minute follow-up call.
Total time commitment from your team: 90 minutes for the assessment + 30 minutes for the findings walkthrough.
"We thought our security posture covered agents because we had DLP. The assessment showed us that our DLP didn't see any of what our Copilot deployment was doing. We had a coverage gap we didn't know existed — and we fixed it before it became a problem."
— Director of IT, Mid-Market Financial Services Firm
What Organizations Without This Assessment Are Discovering
- Agent-accessible data that bypassed DLP policies for months before anyone noticed
- Compliance gaps surfaced during audits rather than internal assessments — at the worst possible time
- Sensitive data patterns extracted by agents and surfaced to users who shouldn’t have seen them
- No audit trail when regulators or clients asked what the agent accessed
These scenarios are drawn from publicly documented AI governance incidents and regulatory findings.
Assessment spots for April are limited.
Steven conducts each assessment personally. That means the number of assessments that can be completed in a given month is finite. If you’re planning an agent deployment in Q2, the time to assess is now — not after you’ve already deployed.
Get Your Free AI Readiness Assessment
Tell us about your organization. Steven will reach out within 24 hours to schedule your 90-minute assessment session. No sales pitch on the call — just a direct conversation about your current security posture and what the assessment will cover.
What happens after you submit:
- You receive a confirmation email immediately
- Steven emails you personally
- You schedule your 90-minute assessment session
- You receive your findings report within 5 business days

Steven R. Combs | Co-Founder & Managing Director, Cocha Technology
Steven is a fractional CIO/CISO with 30+ years of enterprise IT and security leadership. He has built AI governance frameworks for organizations with 1,700+ users, led enterprise Microsoft Copilot deployments, and conducted security assessments across law firms, energy companies, financial institutions, and PE-backed manufacturers. He holds certifications in Varonis, Check Point, FinOps, and Microsoft 365 security, with CISSP certification expected May 2026.
View full profile | LinkedIn