The Law Firm AI Roadmap: A 3-Step Strategy for Data Loss Prevention
February 25, 2026
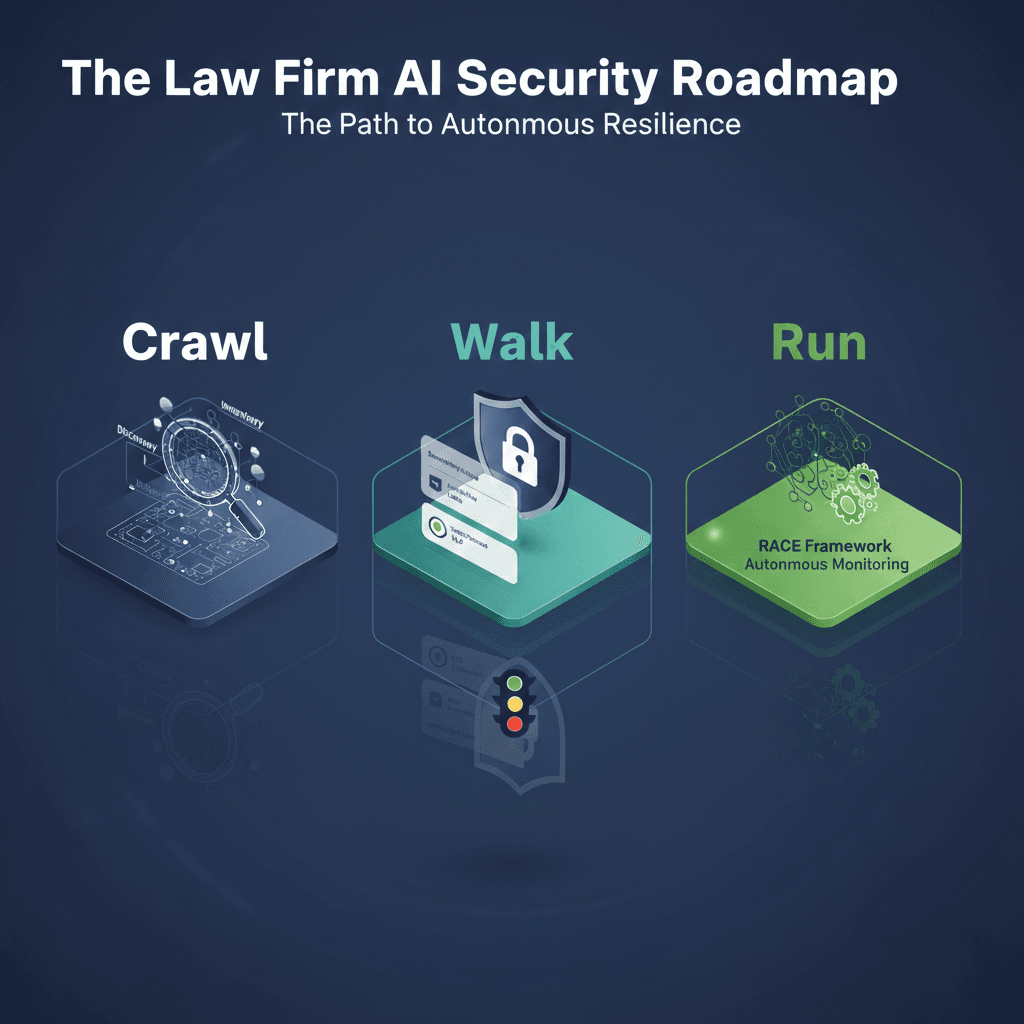
To finalize this series, we must integrate the strategic insights from our previous deep dives into a comprehensive roadmap for Data Loss Prevention (DLP) and AI readiness. This journey began by dismantling the “Permissions Debt” myth; you don’t need to fix 20 years of messy data before starting, but rather you need Containment by Design to innovate on one track while cleaning up on the second. We then moved from “security as a feeling” to a deliberate configuration where a safe launch requires Identity Gatekeepers, Semantic Firewalls, and the RACE framework to ensure the AI isn’t “right for the wrong reasons”. Finally, we identified that legacy data acts as a professional “truth serum” for your firm, making Microsoft Purview the primary tool for pruning “ROT” (Redundant, Obsolete, Trivial data) and preventing the “hallucinations of omission” that stem from a toxic data environment.
The Strategic Pivot: Ransomware Defense is AI Readiness
In the modern legal environment, perimeters are obsolete, and CIOs face a burgeoning “Data War” where clients view their data as a strategic corporate asset. The core strategic insight of the “Cocha Way” is that ransomware defense and AI readiness are the same project because data sprawl—the “AI Danger Zone”—is the technical root cause of both. Currently, 74% of ransomware cases prioritize data exfiltration over simple encryption, largely because “messy” data left in the open is easy to weaponize.
When sensitive information is scattered across unsecured file shares or rogue folders, it provides a playground for both external attackers and internal generative tools. By fixing data sprawl, you solve the Data Loss Prevention challenge for both threats simultaneously. As outlined in the ENISA Threat Landscape 2025, the convergence of AI-assisted social engineering and automated exfiltration means that “static” security is no longer enough; ransomware remains at the core of intrusion activity, with threat groups rapidly weaponizing vulnerabilities within days of disclosure. You must turn your data from a liability into strategic infrastructure by enforcing governance at the source.
Phase 1: Crawl (Discovery & Inventory)
You cannot secure what you cannot see. The “Crawl” phase uses automated engines within Microsoft Purview to map sensitive PII and privileged “client-confidential” data locations across SharePoint, OneDrive, and file shares. This initial diagnostic process scans for “overshared data” and security gaps that have existed for years under the guise of “security by obscurity”.
However, CIOs must avoid the “Anonymization Fallacy”. Many firms believe de-identification is a “get out of jail free” card, but according to the latest research in the 2026 Data Law Trends, traditional techniques are increasingly vulnerable to re-identification due to the sheer volume of external data available to AI. In the legal world, where case details are highly specific, anonymization is a dynamic, context-specific discipline rather than a one-off fix.
The goal of this phase is a comprehensive AI Security scorecard that identifies “Shadow AI” usage—attorneys bypassing security controls to use unauthorized public tools. This provides the baseline needed to transition users to secure, closed-loop solutions.
Phase 2: Walk (Automated Enforcement)
Once the terrain is mapped, we transition to automated enforcement. This involves applying sensitivity labels and Traffic Light Protocols (TLP) to automate Data Loss Prevention. These labels act as a “Semantic Firewall,” ensuring Microsoft 365 Copilot honors data boundaries and ethical walls by default.
To harden this layer, IT teams should implement “Instruction Layering.” This technical safety net involves configuring the AI to follow explicit constraints—limiting its reasoning to verified, “live” databases and preventing it from “compulsively completing patterns” based on toxic legacy data. As noted in the OWASP Top 10 for LLM Applications v1.1, “Sensitive Information Disclosure” (LLM06) is a major risk where models inadvertently reveal confidential data in responses. By layering instructions that prioritize internal Microsoft Purview labels over user prompts, you mitigate the risk of “Contextual Override” where a model might favor a local prompt over established governance.
Phase 3: Run (Autonomous Operations)
At enterprise scale, manual oversight is impossible; AI Security must be enforced through automated Data Security Posture Management (DSPM). In this phase, we operationalize a self-correcting backbone using the RACE (Reasoning and Answer Consistency Evaluation) framework.
RACE ensures the system isn’t “getting the right answer for the wrong reasons”. For example, an AI might correctly flag a document for review but cite a completely fabricated regulatory clause in its reasoning. By tracking reasoning trajectories and measuring Expected Calibration Error (ECE), we identify “confidently wrong” outputs where the model’s predicted confidence disconnects from its actual accuracy.
This provides the “Technical Truth” needed to satisfy forensic-level governance for data lifecycle logs. As the refreshed COSO Internal Control Framework highlights, organizations must transition from periodic reviews to ongoing monitoring, using automated workflows and real-time alerts to manage risk as technology and regulations evolve.
Lead Your Firm into the AI Era
The only path to long-term productivity and AI Security is this phased approach: assess first, scale slowly, and automate governance. By following these 4 steps to deploying DLP, you transform AI from a source of liability into a governed, high-performance tool for organizational growth.
Secure Your Data. Empower Your Practice.
Don’t let data sprawl surrender your competitive edge. Cocha Technology combines veteran leadership with a nimble model to deliver a Data & AI Readiness Assessment in under a month. Our fixed-fee strategic sprint provides total visibility into your data blind spots, identifies “Shadow AI” leaks, and delivers a clear roadmap to close your governance gaps.
Turn your data liability into strategic infrastructure.
Ransomware defense and AI readiness are the same project. If you’re ready to fix data sprawl and secure your firm’s most valuable corporate assets, let’s build your “Crawl, Walk, Run” roadmap together. Connect with a Cocha Strategist or fill out the form below to receive your initial scorecard and move your firm toward the Plateau of Productivity.
Recent Posts
Have Any Question?
Call or email Cocha. We can help with your cybersecurity needs!
- (281) 607-0616
- info@cochatechnology.com

