Trust nothing. Verify everything. Protect everywhere.
In a world without perimeters, your identity is your new firewall. We help you move beyond outdated VPNs to a modern Zero Trust architecture that secures every user, device, and connection—no matter where they are.
Are you dealing with:
The Perimeter Fallacy
You’re still relying on a "strong password" and a VPN, even though you know that once a hacker gets past that one front door, they have the keys to your entire network.
The Remote Work Strain
With a team spread across different locations and devices, you’re struggling to verify access without making the login process a total headache for your employees.
The Lateral Movement Fear
You worry that a single compromised laptop in a junior department could lead to a total breach of your most sensitive financial or executive servers.
Let Us Help
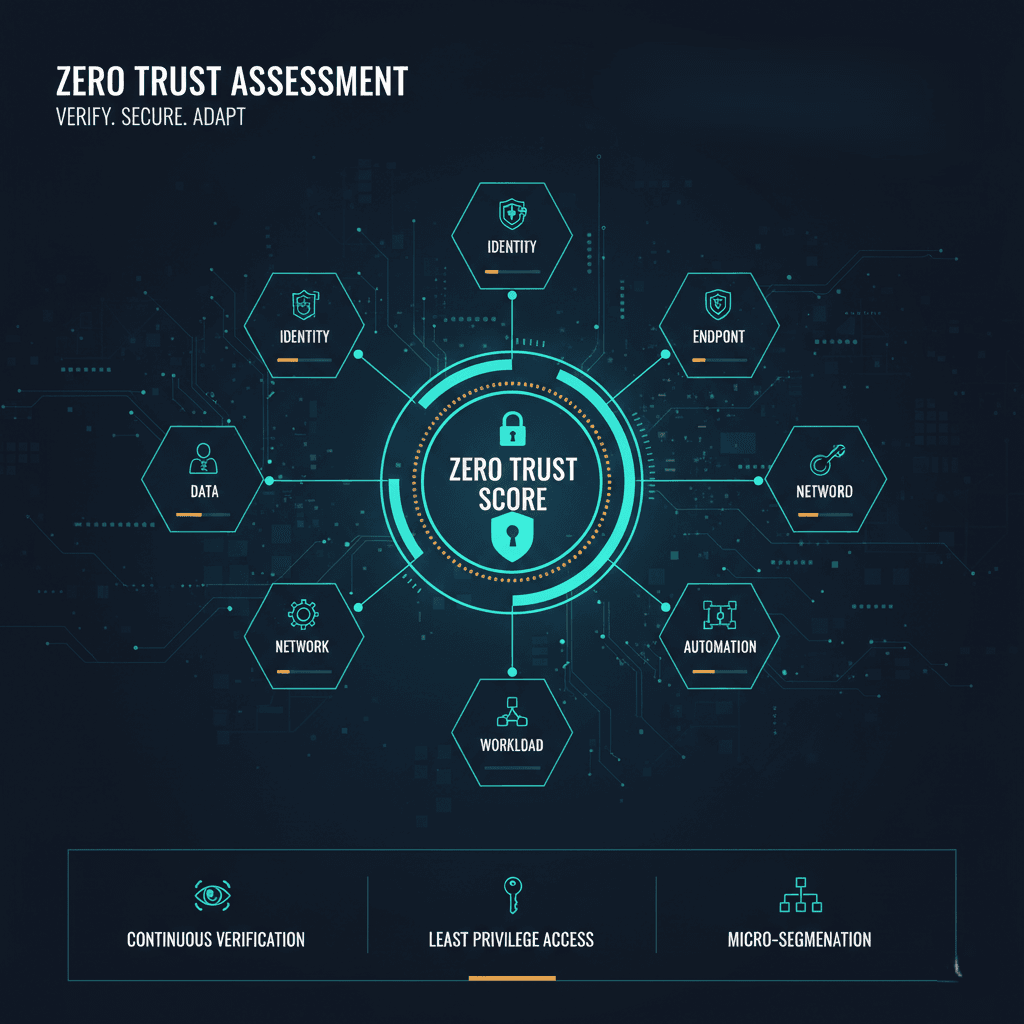
- Ironclad Identity (Unified MFA): We implement multi-factor authentication that actually works, ensuring that only the right people get in without frustrating your team’s daily workflow.
- Contained Risk (Micro-Segmentation): We isolate your most critical assets into “secure zones,” so even if one device is compromised, the threat cannot spread to the rest of your business.
- Precise Access (Least-Privilege Policy): We ensure every user has exactly the access they need for their specific job—and nothing more—minimizing your internal attack surface.
- Real-Time Verification (Continuous Authentication): Security that doesn’t sleep; we move you to a system that verifies trust at every step of a session, not just at the initial login.
The Cocha Advantage
At Cocha Technology, we specialize in phased Zero Trust transitions. We understand that you can’t just flip a switch and lock every door overnight. Our approach is surgical—we identify your highest-risk gaps first and build layers of security that feel natural to your users while remaining bulletproof to intruders.
Strategic Phasing: We build your roadmap in stages to ensure zero disruption to your daily business operations.
Vendor-Agnostic Expertise: We don’t push specific software; we find the Zero Trust tools that actually fit your existing tech stack.
Culture-First Security: We focus on a “frictionless” experience, so your team stays secure without feeling like they’re being slowed down.
Three-Steps to Success
Stop Hoping Your Firewall Is Enough
A 30-minute Zero Trust Assessment can reveal exactly where your ‘front door’ is left unlocked. Let’s build a defense that moves as fast as your business does.





