Protecting Against Birthday Attacks
July 14, 2023

Birthdays are a time for celebration, but they can also attract the attention of cybercriminals who seek to exploit this personal milestone for their malicious purposes. Birthday attacks, in the context of cybersecurity, refer to specific types of attacks that exploit vulnerabilities associated with birthdays or birthdate-related information. In this blog post, we will delve into the concept of birthday attacks, understand their implications, and provide practical tips to protect yourself from falling victim to these cyber threats.
Understanding Birthday Attacks
Birthday attacks are centered around the concept of cryptographic hash functions. A cryptographic hash function is a mathematical algorithm that takes an input (e.g., a string of characters) and produces a fixed-size output called a hash value. Birthday attacks exploit the probability of finding two inputs that produce the same hash value, which is higher than one might expect due to the birthday paradox.

Implications of Birthday Attacks
Birthday attacks have significant implications in various areas of cybersecurity, including password security, digital certificates, and cryptographic protocols. Consider the following scenarios:
- Password Attacks: Cybercriminals may attempt to exploit weak password storage practices or flawed hash functions to find collisions (two different passwords that produce the same hash value). This enables them to gain unauthorized access to user accounts.
- Digital Certificate Collisions: In the context of digital certificates, where hash functions play a crucial role in verifying authenticity and integrity, birthday attacks can lead to forged certificates or compromised security.
- Cryptographic Protocols: Some cryptographic protocols rely on hash functions to ensure data integrity and security. A successful birthday attack on these protocols can compromise the confidentiality and integrity of sensitive information.
Protecting Against Birthday Attacks
While birthday attacks highlight the vulnerabilities associated with hash functions, there are practical steps you can take to enhance your cybersecurity posture:
- Strong Passwords: Use strong, unique passwords that are not directly related to your birthdate or personal information. Avoid using common patterns or easily guessable combinations. Consider utilizing a password manager to generate and securely store complex passwords.
- Multi-Factor Authentication (MFA): Enable MFA whenever possible, as it provides an additional layer of security beyond passwords. MFA requires multiple factors, such as a password and a unique verification code sent to your mobile device, to access your accounts.
- Stay Informed: Stay updated with the latest cybersecurity news and best practices. Educate yourself on the latest hashing algorithms and their vulnerabilities. Being aware of potential threats allows you to make informed decisions and take appropriate measures to protect your digital presence.
- Regular Updates: Ensure your software, operating systems, and security applications are regularly updated with the latest patches and security updates. This helps mitigate known vulnerabilities and reduces the risk of successful attacks.
- Hash Function Selection: If you’re involved in the development or implementation of cryptographic systems, carefully evaluate the hash functions you use. Choose algorithms that have undergone rigorous scrutiny, have a strong security track record, and are recommended by reputable cryptographic experts.
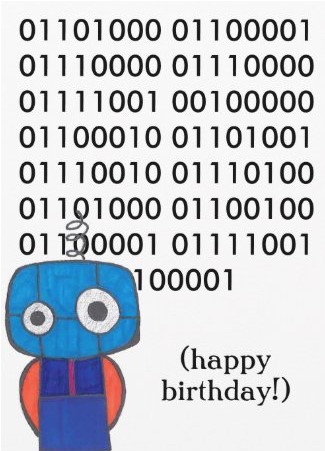
While birthdays are meant to be a joyous occasion, it’s crucial to be mindful of the potential risks associated with birthday attacks in the realm of cybersecurity. By understanding the implications of these attacks and adopting proactive security measures like strong passwords, MFA, staying informed, and keeping your systems updated, you can significantly reduce the likelihood of falling victim to these cyber threats. Let’s celebrate our birthdays while maintaining a vigilant and secure digital presence.
Have Any Question?
Call or email Cocha. We can help with your cybersecurity needs!
- (281) 607-0616
- info@cochatechnology.com