FREE ASSESSMENT
Your Agent Is Secure. Your Infrastructure Isn't.
Agents inherit permissions. That means every overprivileged account, every forgotten shared folder, every broken permission inheritance in your environment becomes the agent's attack surface. Zero trust isn't a nice-to-have before agent deployment. It's the foundation.
✓ Optional CISA tooling for live Entra data
✓ 90-minute session
✓ Findings in 3–5 business days
of organizations currently meet the full definition of zero trust security
Source- PacketLabs, 2023
of companies will choose zero trust over VPNs by 2025
Source- Gartner
of workers use unapproved AI tools — each one inheriting their full permissions
Source- UpGuard, 2025
The Problem Isn't Agents. It's What They Inherit.
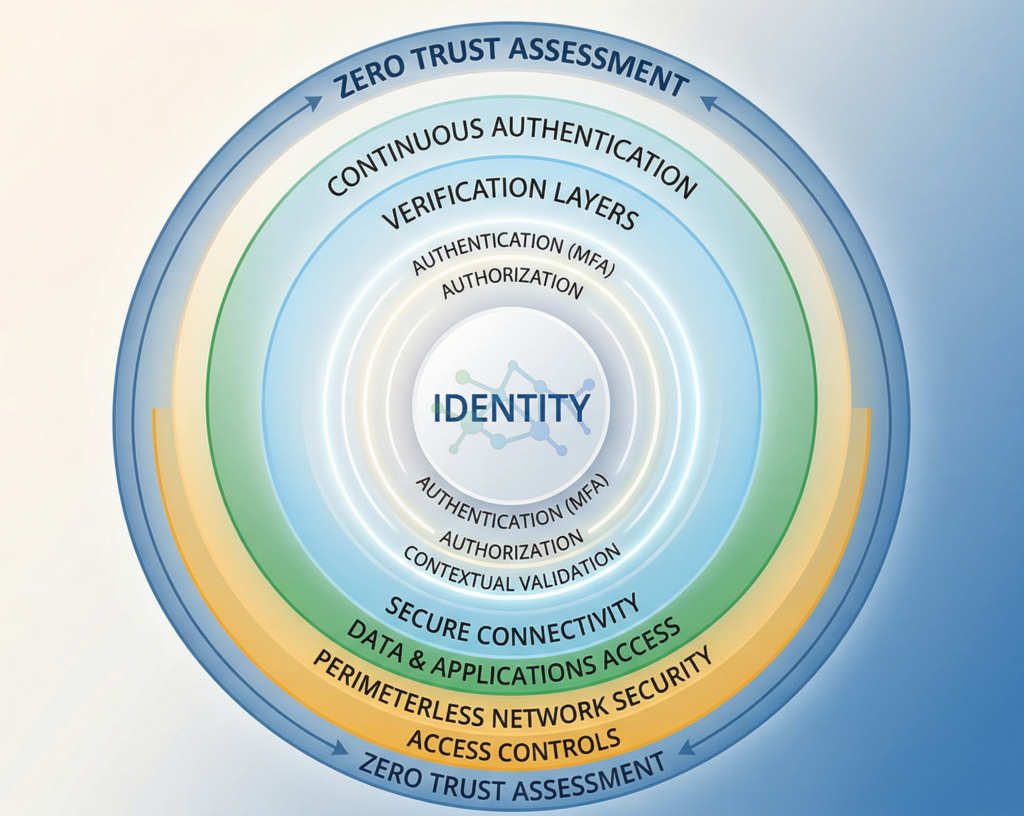
Zero trust security is built on a simple principle: never trust, always verify. No user, no device, no application gets access to anything just because they’re inside the network. Every access request gets verified. Every privilege gets scoped to exactly what’s needed and nothing more.
Most organizations know they should implement zero trust. Most haven’t.
Not because they don’t understand the value — they do. But because getting there requires knowing your current permission state, which most organizations genuinely don’t know. How many accounts have access to the CEO’s OneDrive? How many folders are open to everyone in the organization? How many users still have permissions from roles they left two years ago?
Before AI agents, these gaps were annoying but manageable. Humans are lazy readers. An employee with overprivileged access to a confidential folder rarely reads every file they can access. They’re busy. They have judgment. They don’t go looking for data they’re not supposed to have.
Agents are none of those things.
An agent with overprivileged access will read everything it can reach. It will extract patterns, surface insights, and use that information in its responses. It doesn’t know the data is sensitive. It just knows it has permission.
Every zero trust gap in your infrastructure becomes an agent security gap the moment you deploy.
“Every zero trust gap in your infrastructure becomes an agent security gap the moment you deploy.”
What Agents Find in an Infrastructure Without Zero Trust
Overprivileged Accounts
Users accumulate permissions over time through role changes, project assignments, and administrative shortcuts. Nobody goes back to remove the old access. An agent operating under an overprivileged account can reach data across multiple departments, systems, and sensitivity levels — far beyond what any single role should access.
Broken Permission Inheritance
In SharePoint and OneDrive environments, permission inheritance gets broken when administrators manually set permissions at the subfolder level. The result is a permission map nobody fully understands. Some sensitive subfolders are less restricted than their parent. Some users have access through inheritance chains nobody remembers setting up. Agents navigate this map systematically.
Stale Access From Former Roles
The average organization has a significant percentage of active users with permissions from roles they no longer hold. A paralegal promoted to attorney three years ago may still have access to the paralegal shared drive. A contractor who finished a project in 2023 may still have guest access to a SharePoint site. Agents don't differentiate between intentional access and forgotten access.
Missing Identity Verification
Zero trust requires continuous verification of identity — not just at login. Many organizations still rely on single-factor authentication for shared service accounts, admin accounts, or legacy system integrations. If an agent operates through a compromised account with no MFA, there is no second check.
Get Live Data on Your Entra Identity Posture
For organizations that want objective, real-time data rather than self-assessment estimates, we can deploy CISA tooling into your Entra ID environment as part of the assessment. This gives us live visibility into your actual identity posture — not what your policies say should be happening, but what is actually happening.
CISA (Cybersecurity and Infrastructure Security Agency) provides government-grade assessment tooling that is used by federal agencies to evaluate zero trust maturity. We bring the same capability to your environment.
CISA tooling deployment is optional and requires your explicit consent. It is read-only and leaves no persistent footprint. Deployment and removal take under 30 minutes.
What Your Zero Trust Assessment Includes
Assessment Areas:
- Permission Baseline Audit — We map your current permission distribution across Microsoft 365, SharePoint, OneDrive, and connected systems. How many accounts have privileged access? How is it distributed? Where are the highest concentrations of risk
- Over-Privilege Analysis — We identify accounts with permissions beyond what their current role requires, with specific attention to shared service accounts and legacy access patterns that agents are most likely to exploit.
- Identity Verification Review — We evaluate your authentication posture: MFA coverage, conditional access policies, admin account protections, and service account security. We identify where single-factor authentication creates agent-accessible attack surfaces.
- Monitoring and Audit Trail Assessment — We determine what your current logging captures, what it misses, and whether you could reconstruct what an agent accessed after the fact if you needed to. Most organizations cannot.
- Network Segmentation Evaluation — We assess whether your infrastructure isolates sensitive resources or whether agents with access to one system can pivot to others through flat network architecture.
- Remediation Roadmap — Every finding is ranked by risk and paired with a specific remediation action. You leave with a prioritized 6-month plan organized by effort and impact.
After Your Assessment, You’ll Have:
- Your permission baseline — current state, not what you think it is
- Your over-privilege percentage — how exposed you actually are
- Identity verification gaps — where authentication fails
- Monitoring blind spots — what you can’t see right now
- A 6-month remediation plan with clear priorities
- The evidence you need to justify the investment internally
How the Assessment Works
Schedule
Submit the form below. Steven contacts you within 24 hours to schedule your 90-minute assessment session. If you'd like CISA tooling deployed, we discuss timing and consent in this initial call.
Assess
In a 90-minute working session, we review your permission structure, identity verification posture, monitoring coverage, and network segmentation. If CISA tooling is deployed, we review live Entra data together.
Deliver
Within 3–5 business days, you receive a written findings report with your zero trust maturity score, gap analysis, and prioritized 6-month remediation roadmap. We walk through it on a 30-minute follow-up call.
Why Zero Trust Matters Differently by Industry
PE-Backed Companies:
PE buyers now assess zero trust posture as part of standard due diligence. If agents can’t be deployed safely post-acquisition, it blocks the operational efficiency playbook — and becomes a material risk in valuation. Getting your assessment done before the buyer asks is a strategic advantage.
Medical Device:
The FDA expects zero trust principles in your data access controls as part of AI governance. If you deploy agents in a medical device environment without a documented permission baseline, you’re creating compliance exposure that will surface during an inspection — not before it.
Oil & Gas / Energy:
FERC cybersecurity requirements for energy infrastructure apply to systems that agents interact with. Agents operating in environments without verified access controls create compliance gaps that can’t be papered over after the fact.
"We had no idea how many accounts still had permissions from roles people left two or three years ago. The assessment didn't just find the problem — it showed us exactly what to fix first so that our Copilot deployment wouldn't inherit two years of permission debt."
VP of Operations, PE-Backed Professional Services Firm
Get Your Free Zero Trust Assessment
Tell us about your environment. Steven will reach out within 24 hours to schedule your 90-minute assessment session. If you’d like CISA tooling for live Entra data, let us know below and we’ll discuss it on the scheduling call.
Process summary:
- Submit the form
- Steven emails you
- Schedule your 90-minute session
- Receive your findings report within 5 business days

Steven R. Combs | Co-Founder & Managing Director, Cocha Technology
Steven is a fractional CIO/CISO with 30+ years of enterprise IT and security leadership. He has built AI governance frameworks for organizations with 1,700+ users, led enterprise Microsoft Copilot deployments, and conducted security assessments across law firms, energy companies, financial institutions, and PE-backed manufacturers. He holds certifications in Varonis, Check Point, FinOps, and Microsoft 365 security, with CISSP certification expected May 2026.
View full profile | LinkedIn





